There are various articles explaining what App Only Policies are and how they work with SharePoint Provider Hosted Apps. Two of the good starting points, I found are this msdn blog and this msdn article.
The process of setting is App only permission is really simple. All you need to do is change the AppManifest.xml file.
<AppPermissionRequests AllowAppOnlyPolicy="true">
<AppPermissionRequest Scope="http://sharepoint/content/tenant" Right="FullControl" />
</AppPermissionRequests>
The problem is if you need tenant level permissions for your app, you can’t register the app principal in any of the site collections, like you would do for any other level of permission requirement like Site Collection admin.
Steps to provide tenant admin permission for app only add-in:
- Register app id for the add-in under normal site collection in the tenant where add-in will be deployed.
- URL: https://[tenant].sharepoint.com/_layouts/15/appregnew.aspx
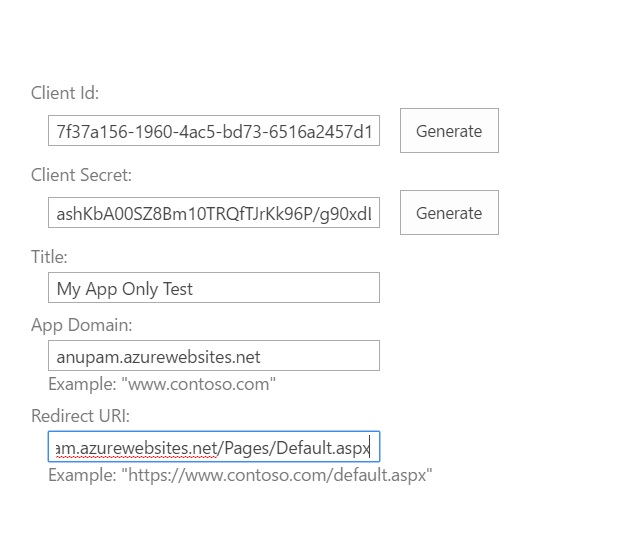
- Provide necessary details for the add-in registration and register ID and secret for your add-in in the Provider hosted app web.config file
<appSettings>
<add key="ClientId" value="7741f989-2668-4e81-b6d4-9364e4c6cfe6" />
<add key="ClientSecret" value="xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx" />
</appSettings>
- Update the Client ID in your AppManifest.xml file
<AppPrincipal>
<RemoteWebApplication ClientId="7741f989-2668-4e81-b6d4-9364e4c6cfe6" />
</AppPrincipal>
- Now comes the change, for any other level of app only permissions (other than tenant level), you would go to
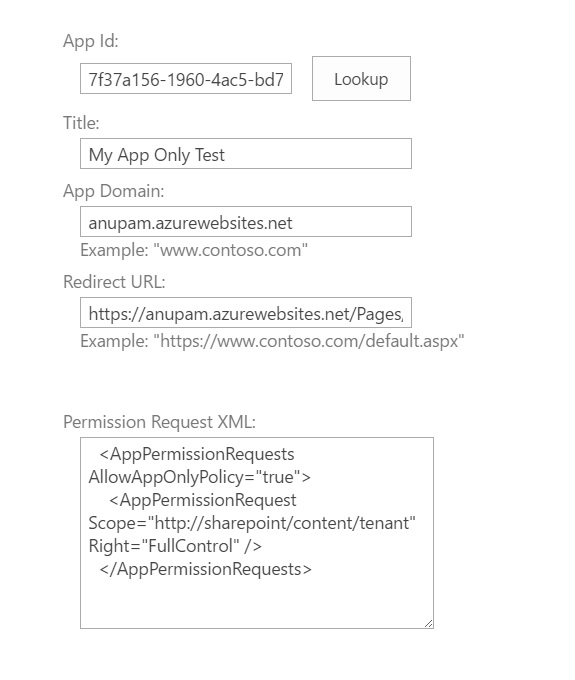
- https://[tenant].sharepoint.com/_layouts/15/appinv.aspx
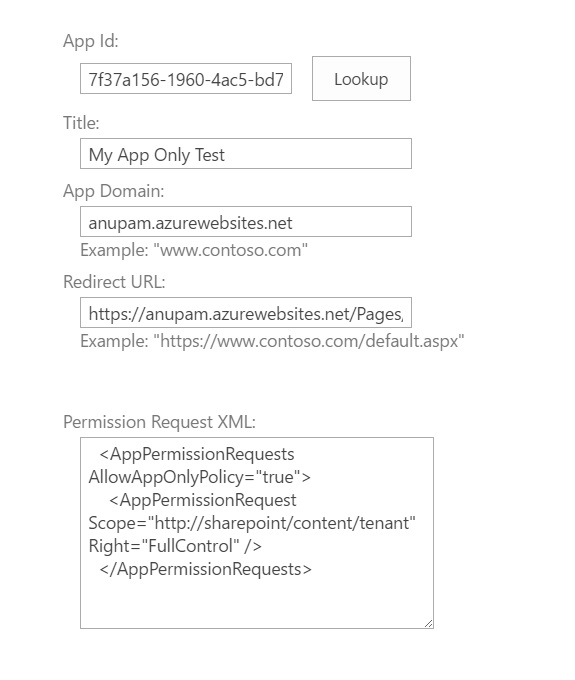
- Perform a lookup on the client ID, you would get the details you provided while registering the app
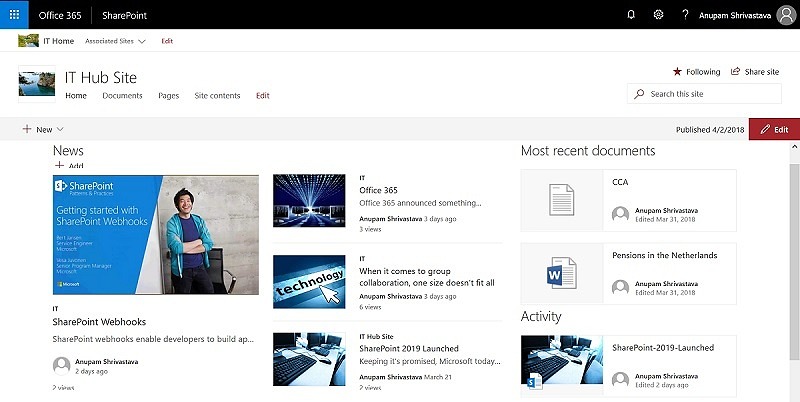
- Paste the XML snippet from AppManifest.xml in the Permission Request XML box. The form would look like this
-
- Click on create, but wait, it shows a message on the next page “Your tenant administrator has to approve this app”! and Trust it button is disabled.
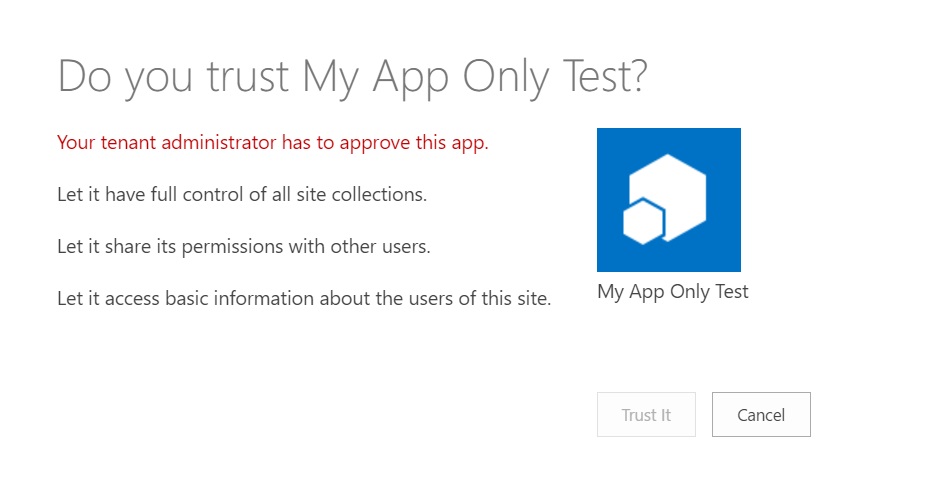
-
- Go back to previous page and try changing the permission to something less than a tenant level permission, like site collection admin, like this and try adding this to the Permission Request XML box and click create
<AppPermissionRequests AllowAppOnlyPolicy="true">
<AppPermissionRequest Scope="http://sharepoint/content/sitecollection" Right="FullControl" />
</AppPermissionRequests>
-
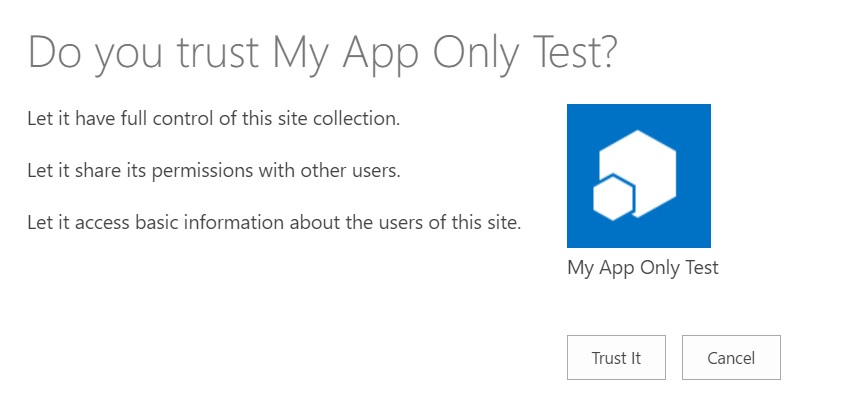
- And this time you would see, no error message and Trust It button enabled too
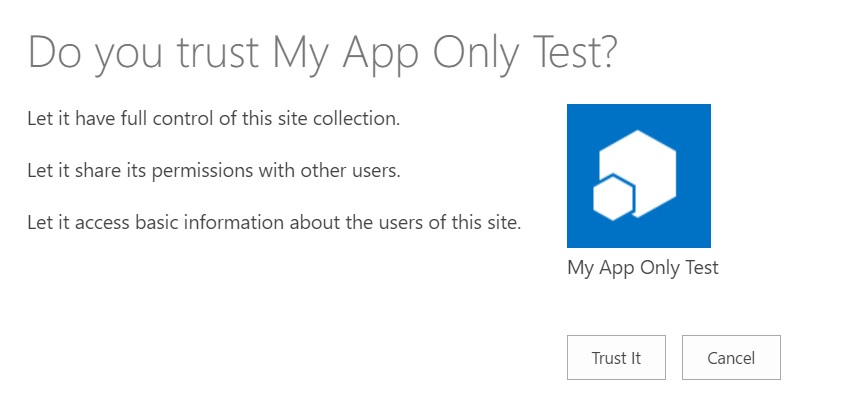
-
- So what changed? Well, MS has recently made a change, which seems to have gone quietly. If you need any tenant level permission for your App only provider hosted app, you need to add permission in tenant admin site and not in any of the site collection! Well lets try that then…
- Go to appinv.aspx page under your tenant admin site
- URL: https://[tenant]-admin.sharepoint.com/_layouts/15/appinv.aspx
- Perform a lookup for the app id registered in previous steps in appinv.aspx page
- Provide needed tenant level permissions for your add-in registration in the Permission request XML box
- On click of Create button, now you won’t see any message on next page. Perform trust for the updated add-in registration
And that’s it your app is registered with ACS to make a call to SharePoint online with Tenant Admin permissions.
A little change is required to get the client context though –
private static ClientContext GetClientContext(string url)
{
Uri siteUri = new Uri(url);
//Get the realm for the URL
string realm = TokenHelper.GetRealmFromTargetUrl(siteUri);
//Get the access token for the URL.
// Requires this app to be registered with the tenant
string accessToken = TokenHelper.GetAppOnlyAccessToken(
TokenHelper.SharePointPrincipal,
siteUri.Authority, realm).AccessToken;
var clientContext = TokenHelper.GetClientContextWithAccessToken(siteUri.ToString(), accessToken);
return clientContext;
}
Just pass in any site URL there and perform any action, it will work as if a tenant admin is performing those tasks like creating a site collection.
Enjoy!
16 comments
this whole process of adding the properties that I should have access to using the xml, then clicking on create and check the disable button and then go back and redo the process again didnt work for me. It shows the same disabled button.
Hi Paulo,
Did you add that xml in the SharePoint Admin Center site?
Hi, Anupam!
If by SharePoint Admin Center um mean adding the xm to the ‘Permission Request XML’ box, yes. I’ve tried with appPermissionRequest – Scope: tenant and Right=”Read”. And then after seeing the error message. I’ve changed to Scope=”http://sharepoint/content/sitecollection” that also lead me to the same error message screen.
Thanks for the reply.
Try generating a new client ID and add that with
AppPermissionRequest Scope=”http://sharepoint/content/sitecollection” Right=”FullControl”
I understand, you are just trying to create a site collection scoped policy. If you want tenant level permissions, you need to add this under SharePoint Admin Center – https://[tenant]-admin.sharepoint.com/_layouts/15/appinv.aspx
Hi, Anupam! Thanks for you repply! I actually had this issue resolved by asking one of the tenant admins to trust my app.
Ok great. Ideally for a site collection scoped app, approval from tenant admin is not required.
May i ask something
In my case i just need to break role inheritance of a list item . It asks for permissions. If i use the admin account it works ok.
Logically, in this case, you need to use an account which has “manage permissions” right. That’s why it’s working with site admin account.
In my case i did it and i didn’t get any error. However when i try to execute my query i get an error again regarding permissions.
Please note i’m using remote event receiver
using (ClientContext clientContext = /*clientContextTest*/TokenHelper.CreateRemoteEventReceiverClientContext(properties))
{
string manager2LoginName = “”;
if (clientContext != null)
{
int listItemId = properties.ItemEventProperties.ListItemId;
ListItem currentListItem = clientContext.Web.Lists.GetByTitle(“LeaveRequest”).GetItemById(listItemId);
clientContext.Load(currentListItem);
clientContext.ExecuteQuery();
I think when i get the client context by just giving the url of my sharepoint app , there is an issue afterwards when executing the query.
Any ideas?
Im kinda confused with this. So afterwards we deploy in sharepoint-admin site , then where can we find the app ? I publish the app and upload the app file to my dev site . Then i deploy it using the appinv in tenant site? I’m a bit confused :/
Also is there a way to do debugging ? When i debug it tried to deploy it to my dev site and trust button is disabled
Hi,
I don’t think it’s related to App Only Policy. Better, if you can debug your remote event handler in Dev site first. That’s a bit tricky though. You need to get an Azure Bus service registered. Another alternative is to put a try catch block and write the exception in a text file. Better get it working properly in the dev site and then publish in app catalog.
Hi again.
I do debug it in dev site. However when i debug it , it deploys it and the trust button is disabled. So there is no way to debug it with app only policy and tenant permissions. I can only debug it when i don’t use tenant permissions.
What is the procedure exactly to publish it with app only tenant permissions? I upload the app in app catalog . Then i go to sharepoint-admin site and use appinv.aspx . Then i go to the site where i want to deploy it , and when i add the app is deployed with the correct permissions?
Is this the procedure to follow?
Managed to fix it by Trusting is as an admin. So you add the app to catalog , then deploy it to the site you want and send approval request to the admin to approve it.
However i still haven’t found a way to debug an app that requires tenant permissions , because when you deploy it the Trust button is disabled
Hi Andreas,
Did you find any solution for debugging the app with tenant permissions? Please help me if found
Thanx
Darshani
Hello.
Thanks for the article.
My issue is:
Whatever I put in App permission XML (FullRights), I am always seeing ” Let have basic access..” but no “Let it have full control…” What I did wrong?
All I can suggest is to cross verify if you are providing the xml the tenant admin site – https://[tenant]-admin.sharepoint.com/_layouts/15/appinv.aspx and the XML contains this –
AppPermissionRequests AllowAppOnlyPolicy=”true”
AppPermissionRequest Scope=”http://sharepoint/content/tenant” Right=”FullControl”
AppPermissionRequests